wifi
-
Elements that obstruct the flow of Wi-Fi signals
A WiFi and bluetooth jammer Can Prevent Data Theft
It is important to understand that WiFi is available in 2 frequencies, 2.4GHz and 5GHz. While 2.4GHz is by far the most commonly used, some newer routers do include 5GHz.
Bluetooth is within the 2.4GHz band, so any WiFi jammer that covers 2.4GHz is also going to block Bluetooth.

The next important consideration is the size of the coverage area needed for your application. We offer units such as which covers both 2.4GHz and 5GHz to approximately 15 meters, the popular spy camera jammer which covers 2.4GHz WiFi only to approximately 20 meters, or the extremely powerful TSJ-WiFi-5GH which covers both, up to 250 meters.
There are some variations in the coverage area depending upon local signal strength, physical environment, etc. Where the signal is weaker, the coverage is greater, and vice versa.
How Far Should WiFi Reach?
The range of the WiFi signal may differ due to various factors, such as the frequency range, signal strength, and the presence of walls or obstacles between your jamming device and the router.
The 2.4 GHz frequency band offers improved device coverage, albeit at a reduced speed. Conversely, the 5 GHz frequency band provides faster speeds but has a limited range, thereby optimizing your network's performance.
The range of a standard WiFi router typically extends up to 100 feet indoors and up to 300 feet outdoors in open spaces. Nevertheless, the presence of other devices or materials can cause interference, leading to a notable reduction in this range.
Signal Disturbances and Interference
The WiFi signal enables the connection of your devices to the internet by utilizing a frequency range (2.4GHz or 5GHz) that propagates through the air. Opting for newer equipment that supports the 5 GHz frequency band is crucial due to the shorter range of signals in this band, reducing the likelihood of interference from other networks compared to older equipment operating on the 2.4 GHz band.
Metal
Metal is the primary material that will significantly weaken your WiFi signal. As an exceptional conductor of electricity, it has the ability to bounce back WiFi signals, resulting in buffering while streaming or videoconferencing, delays during gaming, and irritatingly sluggish loading times.
Walls (Concrete & Brick)
The ability of walls to impede WiFi signals is contingent upon several factors, such as the composition and thickness of the wall material.
WiFi signals often face difficulties in penetrating concrete and brick walls. Among the two, concrete walls pose a greater challenge as they have a higher density and thicker mass, making them more effective at blocking WiFi signals compared to brick walls.
Windows, Glass & Mirrors
It’s generally not recommended to place your router next to a window or a mirror, either. WiFi signals can’t pass through windows, glass, and mirrors because these materials contain a thin layer of metal that reflects the radio waves back instead of allowing them to pass through.
PR -
Suspects involved in the break-in are employing cell-jamming technology as a means to evade detection by surveillance cameras
Suspects involved in the break-in are employing cell-jamming technology as a means to evade detection by surveillance cameras.
Cell-jamming employs devices that disrupt radio or wireless signals
CMPD has reported that burglars have managed to outsmart surveillance cameras during certain instances of home break-ins by utilizing advanced technology.

Cell-jamming, also known as signal interference, occurs when an individual utilizes a device to disrupt radio or wireless transmissions.
The Federal Communications Commission has stated that deliberately using a phone-jammer, GPS blocker, or any other signal jamming device to obstruct, disrupt, or interfere with authorized radio communications is considered a breach of federal law. It is important to note that there are no exceptions for using such devices within a business, classroom, residence, or vehicle.
Cellular jamming may be initiated by a device positioned at a distance of around 30 feet from the intended target, or alternatively, by home cameras.
Footage obtained from a residential area in south Charlotte exhibits an individual surreptitiously moving through a backyard during nighttime. However, it is important to note that not all occurrences have been recorded on video.
John Shocknesse, VP of Customer Operations for CPI Security, stated that people will always try to disrupt wireless communication, regardless of whether it is on Wi-Fi or any other network.
Within seconds, a person can be captured on camera, but with the use of cell-jamming technology, a single switch or button press is all it takes for that individual to vanish without a trace.
CMPD has reported that this problem has occurred during several incidents of home break-ins in the southern region of Charlotte.
Shocknesse emphasized that there has been no evidence of such activity. They are actively acknowledging this issue and striving to acquire the most advanced and cutting-edge technology, which holds the highest significance for them.
WBTV questioned him regarding the devices that are highly prone to cell-jamming
Shocknesse stated that the lack of encryption is noticeable in older wireless devices.
According to him, the latest security and surveillance systems incorporate advanced technology with encryption, resulting in enhanced security measures.
Shocknesse emphasized the significance of having cameras and onboard recording, stating that it cannot be stressed enough. The cameras are equipped with memory devices, ensuring that even in the event of a problem, the footage of the incident is recorded and can be presented to the police department.
In addition to his previous suggestion, he recommended that the most effective measures to avoid cell-jamming are to utilize modern technology with encryption and to opt for a wired device instead of Wi-Fi.
To effectively prevent home break-ins, it is advisable to adhere to basic guidelines such as ensuring proper illumination, activating alarm systems, and keeping bushes trimmed to a maximum height of three feet.
-
Thieves in Burglary Wifi Jammers Disable Home Security System
Arrest warrants obtained on Friday revealed that a group of tech-savvy burglars, who have been targeting homes in Connecticut and Massachusetts, gained access to a local residence by obtaining detailed information on the security system from the homeowner's co-worker.
Matthew Colon, a 31-year-old resident of West Springfield, Massachusetts, has been apprehended for his involvement in a conspiracy to commit first-degree burglary and conspiracy to commit second-degree larceny. Similarly, Enrique Santiago, aged 37 and hailing from Springfield, Massachusetts, is facing multiple charges, including first-degree burglary, possession of burglary tools, theft of a firearm, and conspiracy.
According to the warrant for Colon, authorities anticipate apprehending a third individual in relation to the incident. This case is linked to a series of burglaries involving sophisticated surveillance techniques and knowledge of homeowners' absence.
On May 20, 2022, a resident of Green Manor Terrace contacted the police from Long Island, informing them that two men were seen walking through his backyard on a security camera. The officers who intervened in the burglary discovered a broken rear sliding glass door and a series of abandoned evidence near the property, such as a WiFi jammer, a two-way portable radio, a glass punch tool, a pry bar, and bolt cutters, as stated in the warrant.
According to the arrest warrant affidavit written by Windsor Locks Detective Sgt. Jeff Lampson, the thieves managed to breach a chain link fence and disable surveillance cameras using both manual methods and a WiFi jammer. However, one camera near the pool remained unaffected by the gsm jammer device and continued to record. The homeowner reported the theft of US$4,200 in cash, as well as men's watches, jewelry, and his wife's 9 mm pistol.
According to the police, on May 26, a pillowcase was discovered by a resident who lived two houses away. The pillowcase contained watches, a handgun, and other belongings that the victims confirmed as their own. The burglars, after the break-in, fled in separate directions, as indicated by the locations of the bag of stolen items and the backpack containing a WiFi jammer.
On Friday, Lampson stated that the use or operation of jamming devices is prohibited by federal law and federal investigators are showing interest in the matter. He also mentioned that the local police have observed an increase in the use of these devices in residential burglaries.
The thieves' downfall was ultimately confirmed by the police through DNA evidence in this particular instance. While conducting a thorough search of the Green Manor Terrace vicinity on May 23, a resident discovered a previously unseen pair of gloves and promptly handed them over to the authorities. The police then sent swabs from the gloves, along with other potential evidence that the thieves may have come into contact with, to the state forensic laboratory for analysis.
According to the warrant, Lampson wrote that on August 16, the lab reported a DNA match on the gloves to Santiago, which indicated the involvement of an offender. The police stated that the same DNA was linked to two prior burglary cases, one of which was a car break-in in Middletown from 2010, and the other was a burglary in South Hadley, Massachusetts in 2012, where firearms were stolen. Santiago was apprehended in both instances.
According to the warrant, Santiago, through his lawyer, informed the investigators from Windsor Locks that the individual responsible for coordinating the Green Manor Terrace burglary was a man who drove a black sedan and whose father owned a remodeling company. In the same warrant, Lampson stated that when he asked the homeowner if he was familiar with someone fitting that description, the homeowner promptly identified Colon, who happened to be a co-worker at a home health care business in East Longmeadow, Mass.
According to the warrant, the homeowner mentioned that he regarded Colon as a friend and had informed him about his visit to Long Island in May of last year. The victim further stated that Colon and his father had assisted him in renovating his house. The warrant also mentioned that the homeowner stated that Matthew Colon had visited his residence on multiple occasions and was familiar with the surveillance camera system.
Colon explained to the authorities that he was brought into the burglary plan by the third suspect, as stated in the warrant. This revelation came after the victim's statements and burglary evidence were presented to him. The police are currently expecting to arrest the third suspect in the near future.
The girlfriend of the suspect was also employed at the home health care company where Colon and the victim from Windsor Locks worked. According to Lampson's warrant, other employees of the company reported that their homes in Massachusetts had been burglarized. One woman claimed that Colon had visited her house to repair a gazebo before the burglary occurred.
According to the warrant, cellphone records indicated that Colon, Santiago, and the unidentified suspect were in communication before and after the Windsor Locks burglary. The police have identified the third suspect as a convicted felon with an extensive criminal history, which involves armed robbery and multiple burglaries.
Santiago's extensive criminal record, as mentioned in the warrant, includes convictions for burglary and larceny in Connecticut. The Massachusetts investigators suspect his involvement in a criminal organization that specializes in targeted burglaries. Santiago has posted a bond of US$150,000 and is expected to make an appearance in the state Superior Court in Hartford on May 31. Similarly, Colon has posted a bond of US$100,000 and is scheduled to appear in court on May 2.
-
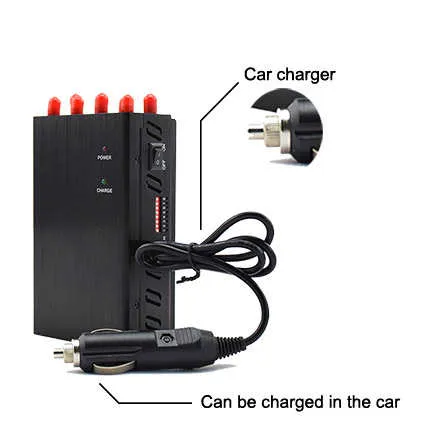
How to jammer all wireless signals?
The so-called signal shielding means that the receiving device cannot obtain a signal with a signal-to-noise ratio that meets the signal identification requirements. Signal to noise ratio (Signal Noise Ratio, SNR) is the most important content.
We can refer to the formula:
SNR = \frac{P_{Signal}}{P_{Noise}}
Therefore, there are two ideas for reducing the signal-to-noise ratio:
- Reduce signal strength
- Increase noise intensity
Based on the above ideas, we can use signal jammers to interfere/shield wireless signals.
The function of a signal jammer is to shield signals and is used in many situations. Nowadays, information spreads very fast. With a mobile device, all kinds of information can be spread to every corner in an instant. For some occasions where information cannot be spread, mobile phone signal cellphone jammer are very necessary.
Within a certain frequency range, mobile phones and base stations are connected through radio waves to complete data and sound transmission at a certain baud rate and modulation method;
Based on the above communication principle, the Dazhan jammer scans from the small-end frequency of the forward channel to the big-end at a certain speed during the working process. This scanning speed can cause garbled interference in the message signals received by the mobile phone. The mobile phone cannot detect normal data sent from the base station, making it impossible for the mobile phone to establish a connection with the base station. Communication equipment exhibits phenomena such as searching the network, no signal, and no service system.
Basic principles of 5G shielding:
Mobile phone signal jammers (jammers) achieve interference and shielding of wireless communication signals by emitting co-channel interference signals. The transmit power of the wifi signal jammer directly affects the strength of the interference signal, thereby indirectly affecting the shielding effect of the signal jammer. There is a positive correlation between these three. In other words, the stronger the transmission power, the stronger the interference signal, and the better the theoretical shielding effect in the same environment.
What factors affect the shielding effect? In the actual use environment, the interference signal emitted by the mobile phone signal jammer is affected by various factors, the most important of which are the following:
- The indoor jammer is recommended to be placed at a height of about 180cm-220cm above the ground, preferably at a forward angle.
- Is there any obstruction (such as walls, metal products, human body, etc.) between the gsm signal jammer and the wireless communication device (mobile phone, etc.). The interference signal emitted by the jammer will attenuate to varying degrees after passing through the obstruction, so please try to avoid it.
- The original wireless communication signal strength in the application environment of the jammer. The weaker the wireless communication signal strength in the use environment, the stronger the theoretical shielding effect of the jammer.
- The distance between the application environment of the jammer and the communication base station. The farther the application environment of the jammer is from the base station, the stronger the theoretical shielding effect of the jammer.
-
Burglary suspect uses cell phone jamming technology bypass surveillance cameras
Cellular interference involves the use of equipment that interferes with radio or wireless signals

Cell destruction can be done with a device placed about 30 feet away from the intended target or via a home camera.
CMPD says thieves have figured out how to bypass security cameras and use technology in some burglaries.
This is called "cell interference" and occurs when a person uses a device to interfere with a radio or wireless signal.
According to the Federal Communications Commission, "It is a violation of federal law to use a phone jammer, GPS blocker, or other signal jamming device designed to intentionally prevent, interfere with, or disrupt authorized radio communications." A business, classroom, residence or vehicle. "
Cell destruction can be done with a device placed about 30 feet away from the intended target or via a home camera.
Video from a south Charlotte neighborhood shows a suspect sneaking through yards at night, but not all of the incident was caught on camera.
"Anytime you have wireless devices, whether it's Wi-Fi or whatever, you know people are going to find a way - how to jam them, how to try to prevent something from communicating," CPI Security Customer Operations said.
Within a few moments, someone is visible on camera, but as cells burst, with the push of a button or button, the person disappears or is not recorded.
CMPD says this problem has been seen in some break-ins in south Charlotte
“We haven’t seen any activity like this, so we’re aware of that and the most important thing is making sure we have the best technology and the latest technology,” Shocknesse said.
WBTV asked him which devices are more susceptible to cellular interference
"I think it will work on some older wireless devices that don't have encryption," Shocknesse said.
Newer security systems and surveillance systems have better encryption and are more secure, he said.
“I really don’t think we can emphasize enough the importance of having cameras and some onboard video,” Shockness said. “The cameras we put in there are equipped with storage so if something goes wrong, you can still record what happened and report it to the police.”
To complement this advice, he said the best solution to prevent cell phone interference is to use current encryption technology and wired devices rather than WiFi.
To prevent break-ins, simple tricks such as maintaining good lighting, turning on alarm systems and trimming shrubs to a height of no more than one meter can be effective.
